Jake AR
@PF-3320 RocketChat ID: 6AZpoAX3J8Pbm3aNr
653 total messages. Viewing 100 per page.
Prev |
Page 4/7
| Next
Sounds good
That is so weird. Can you try it on your PC and phone browser
Screenshot_20211214-141211_Chrome.jpg
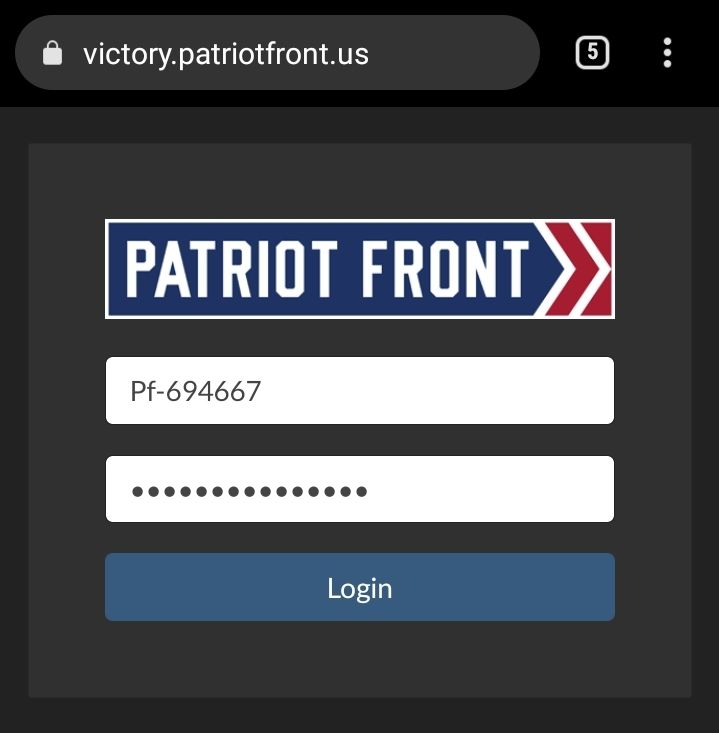
Should look like this
Thanks for testing this out I know others are having similar problems so if we figured this out then it would help everybody
You can do both
Did you still get the error? Did you used to be able to get into victory before? Has anything changed like which phone you're using or browser?
Interesting. Maybe there's something else going on here. The last thing is can you try using a different browser like Chrome on your computer or on your phone using incognito tab.
I saw. I just tried and it worked for me. Using any VPN?
I tried mine with vpn and no issue
Thanks for your help I think I got quite a bit of information I'm going to look at the logs and check with some other users. I'll let you know
@Vincent TX do you have another user that's having the same problem with victory? I was working with Jim ma and he is still having the problem and I can't figure out why.
Also can someone send me the new key for victory through tg or something. I want to know if I can check the logs and see if they're getting errors when they try to log in
Is protonmail even good anymore?
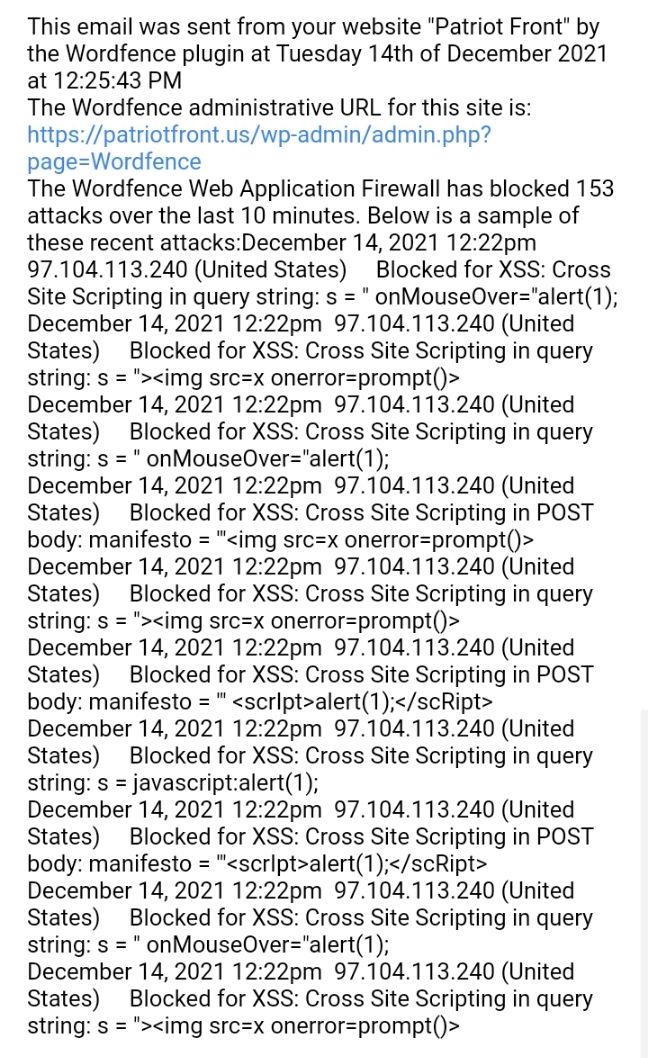
Also this morning the website was attacked.
Screenshot_20211214-154756_Gmail.jpg
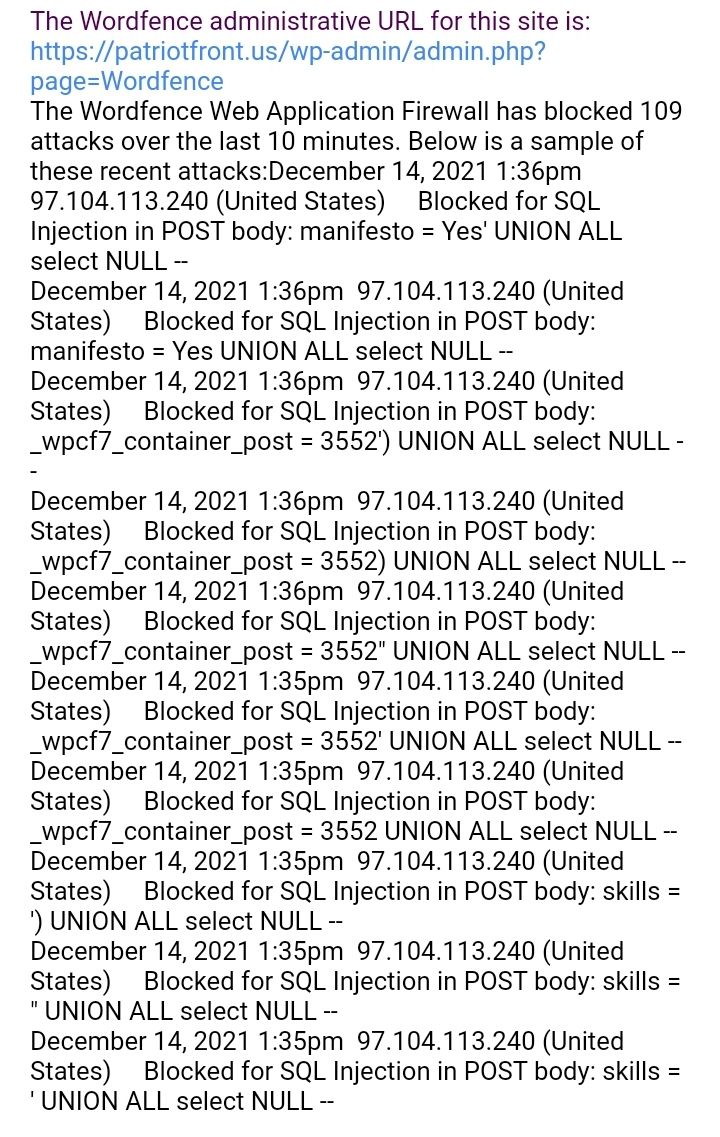
Screenshot_20211214-154843_Gmail.jpg
@Thomas you can check cloudflare to see if there was an increase in any attacks as well
I got the alerts around 7:30 a.m. so maybe it lines up if that's not normal traffic at 9:00 a.m.
The IP address is from Florida 97.104.113.240. I'll look through rocket chat to see if that matches a user
Lmao
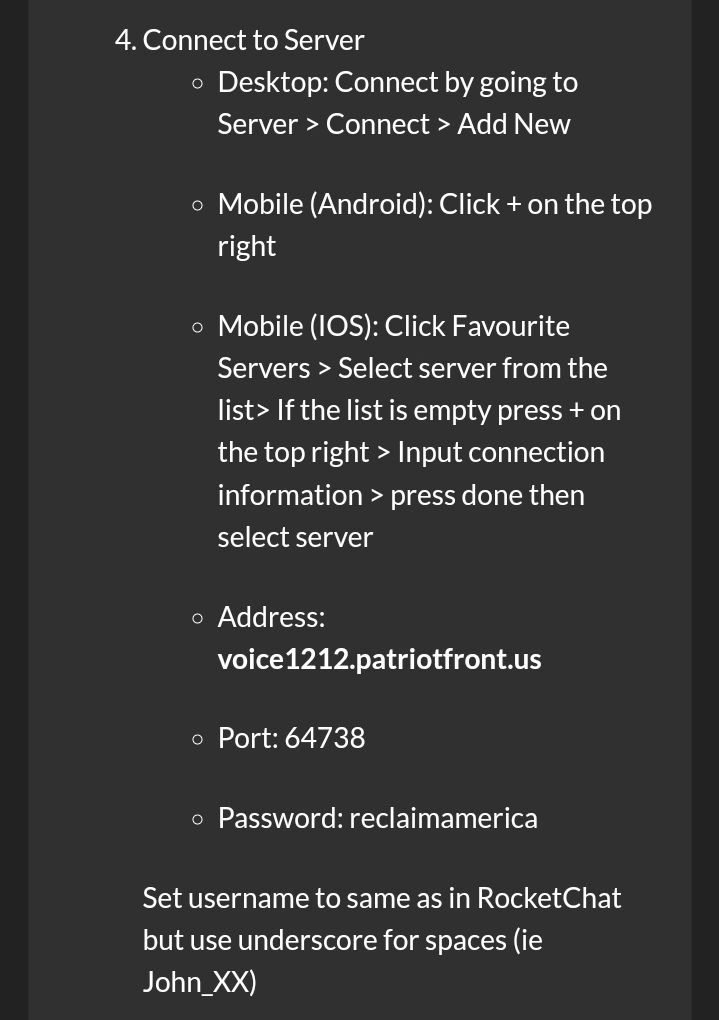
You need to mumble instructions right
Screenshot_20211214-155548_Chrome.jpg
our systems were tested and survived. But we're still in their crosshairs it seems
Yea it's not hard for them to find the subdomains. Is there any sort of system that we should have in place like what we have for the WordPress website that checks and blocks XSS and stuff. I guess we're just relying on rocket chat being built well right?
That might be something to consider
RIP
Does that require the server to be able to communicate to an outside server
Or is it just showing information to the user
Okay. @Vincent TX Let's add looking into a WAF possibly cloudflare for the rocket chat servers
You're welcome. Anyone else you hear that's having problems with victory have them message me
That might not be a bad idea. Victory isn't really too dangerous. Since it is hard coded and only does one thing which is authenticates the user I'm not sure how that could be exploited
I think at worst they could log in as a different user but they would see the same exact thing, right?
Are we thinking they could get in the middle?
Yea, if it's an infiltrator we will definitely catch him
Yea lol probably
It's dated attack
I mean luck and skill
Our servers are locked down well. Idk about victory as much tbh
But we should be doing more.
I agree. @Vincent TX let's add that ^ and log analysis for attacks and vulnerabilities to cryptpad
Don't wanna lose any of these good ideas.
Cool, maybe that's something you can head up on
Sure. For the sake of time. I think it may be helpful to just clone the server and do the step updates because and we don't have to transfer all of the uploads and all the custom scripts and everything else that has got it working to this point. Not looking forward to getting everything back to this current state, even though it'd be a good exercise for documentation on worst case scenarios
@Thomas we need to coordinate sometime this evening for me to remove a couple security features on the main rocket chat server so you can create a snapshot and then I'll turn them back on. I don't believe this is a huge risk because all it's doing is enabling passwords to ssh into server.
That's what we did last time and I think they cleared the keys with the clone because the concept of cloning snapshots I guess is to clone everything but the keys
So since we couldn't log in with a password since the security settings were cloned as well we had no way of getting into it
All right just let me know so I can change the settings right beforehand
That'll be fine
Either now or after we make the clone we should try the cloudflare firewall settings to see if it'll block the app
We'll just have to communicate to people through rocket chat what the new Mumble server is
You can go ahead with the cloudflare firewall rules update.
Also the WordPress plugins are supposed to update regularly and I get alerts if they don't
Also WordPress updates too
Seems to have done it on Android
Screenshot_20211214-172006_RocketChat.jpg
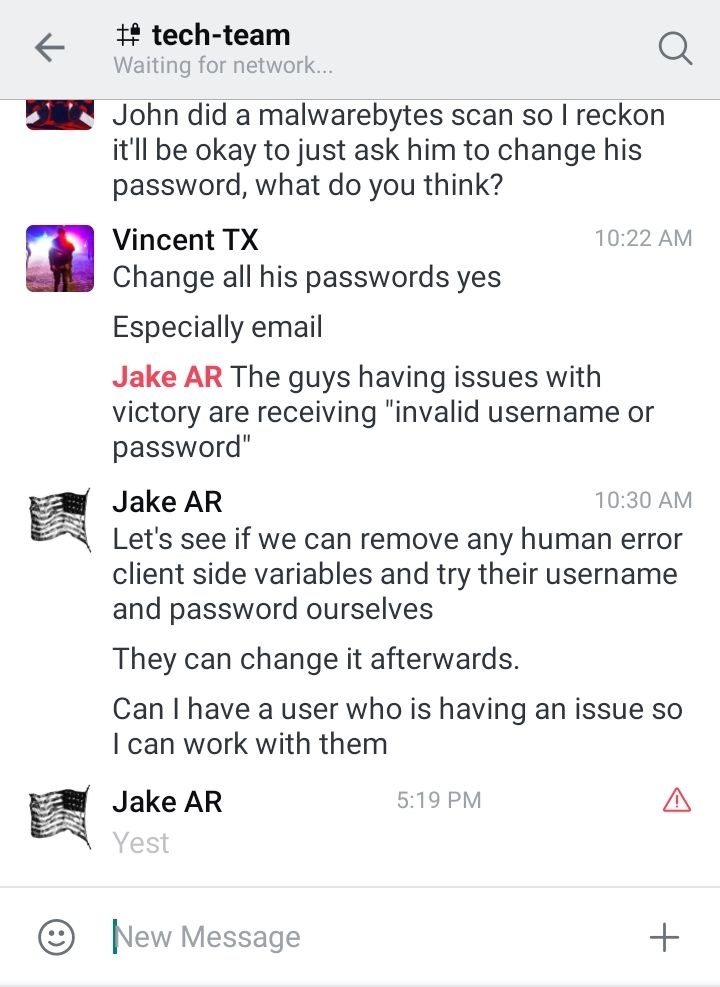
Says waiting for network and won't let you message
Screenshot_20211214-172032_RocketChat.jpg
When you try to log in it gives this error
Well that was easy
Now we find out who has been following instructions
Do we think this is a good idea to also do for the vetting server? Or do we tell the applicants that they can use the app and we need to start phasing out those instructions
The vetting server has working user hash script so it would benefit by having the apps disabled
Yeah I just checked the code it looks good.
We'll see what Thomas wants to do since I don't know if they're supposed to use the app or not
You have to do the same cloudflare firewall rule but for Patriot front us
@Matthew MN suggested we take victory down entirely
I think at 8cst and message Vincent
I think just general concern that it is not secure without a WAF. I am not sure how big of a risk victory being up is
I think we should leave it up and work on getting a WAF for all domains in near future
We dont have a timeline.
Screenshot_20211214-174756_Chrome.jpg

That's what this tasks is. This really isn't related to the API but more detecting and blocking any attacks
Yea. We'll look for a solution soon
@Vincent TX sorry to keep asking me to add stuff but let's add "log monitor for vulnerabilities and atracks with something like greylog"
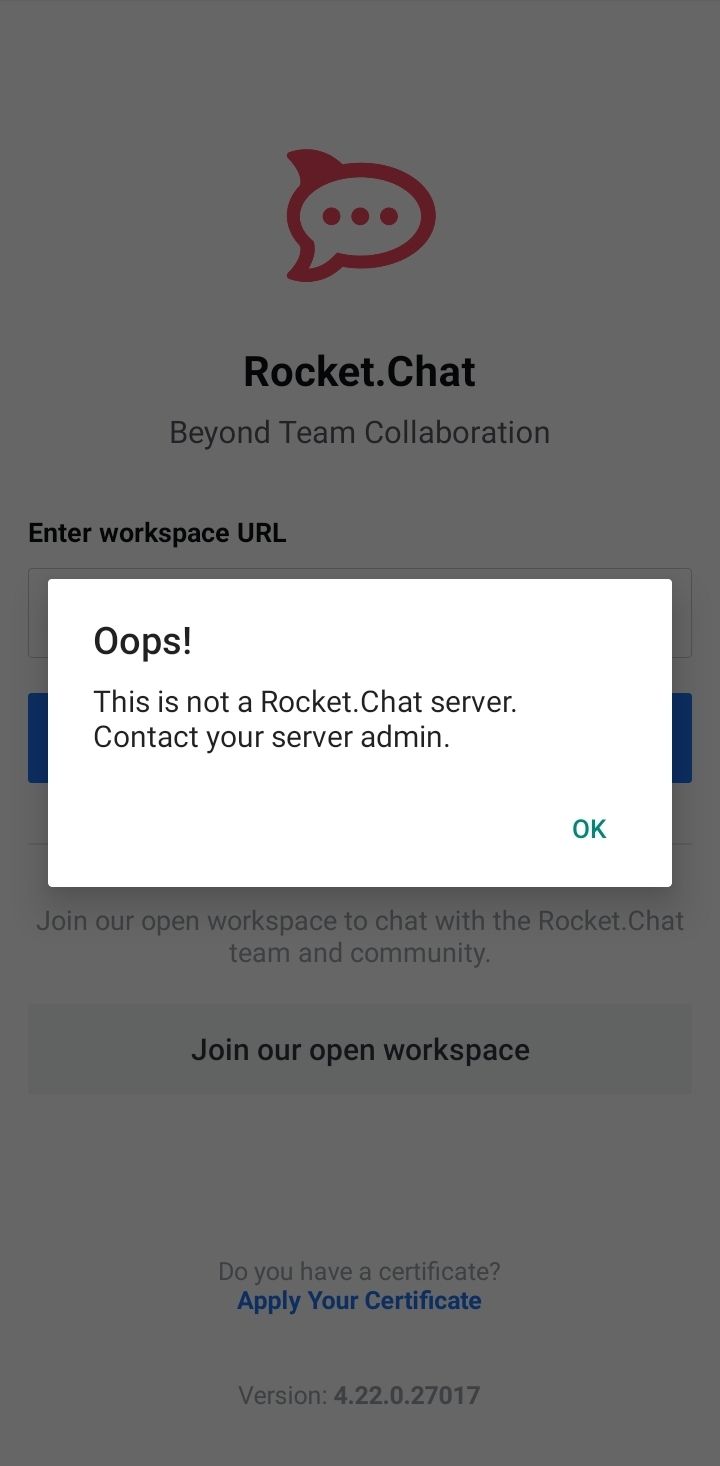
Now that rock attack is entirely based in the browser I think we can increase the cloudflare security. Like when you go to the WordPress website from an out of us IP it does this
Screenshot_20211214-175103_Chrome.jpg
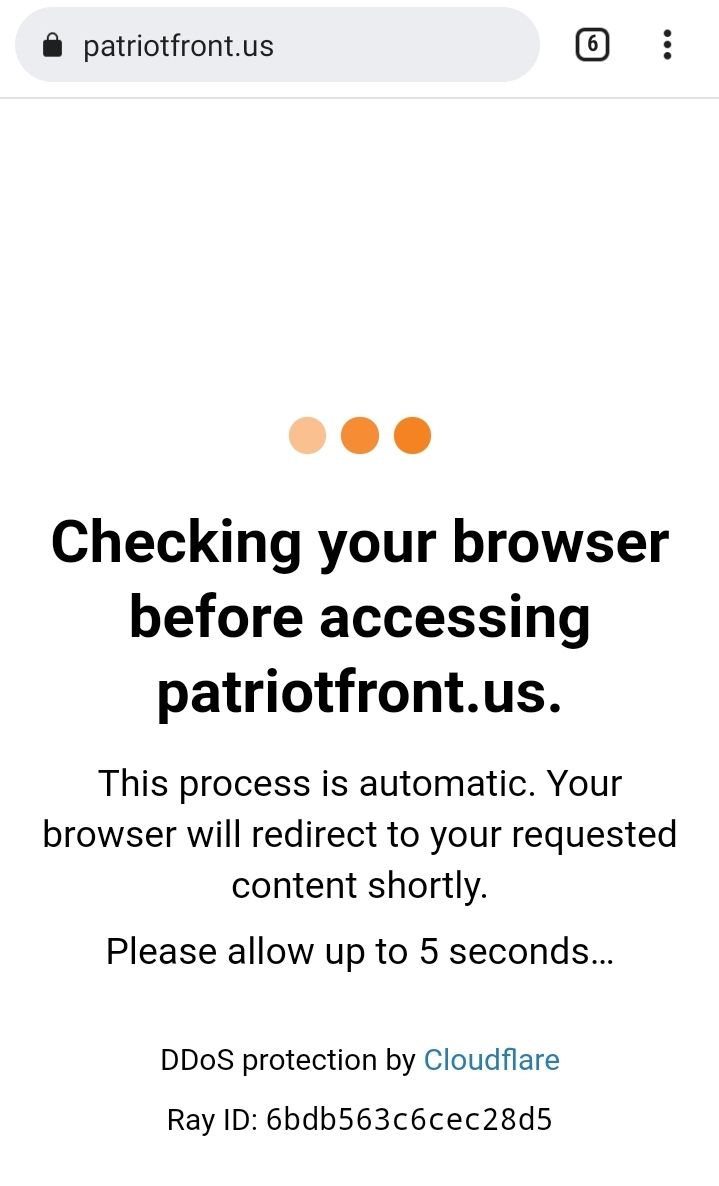
We could do this for both the rocket chat servers and victory from anyone who has an outside of us IP or for any location. It would make it a lot harder to DDos or hammer our api
We can add that as a task as well to strengthen the cloudflare protection On all servers @Vincent TX
Yea me too
You might have to whitelist on cloudflare the victory server so when the victory server tries to communicate with the main server it doesn't have to wait for cloudflare
Nginx and rocketchat
Mostly nginx
Is it possible to run greylog on the same server that it's monitoring
So we can sort of just keep everything contained, then if there is any issues we can have it send messages to the rocket chat server and then just delete any personal identifying information
Since you have some experience with it can you do custom scripting with it like say a log entry comes in and I'm looking for a certain endpoint and I want to process something with the IP address
I don't mind long lists as long as priorities are set.
We're just changing a lot of stuff right now and things are coming up that I don't want us to just forget about
I was wondering if I need to write something custom to monitor the logs because I want to know when someone joins a channel or the server and what IP they're using and what the user agent is and if they go to a different channel I want to do something with that too
I was going to write some crazy regular expressions for each added line to the log file and just try to monitor it somehow
Cool, well I'll have to kind of work on this one together. What I think would be most ideal is if we had a central channel that all of these logs were processed and then put into so I could go into this channel and rock a chat and search for a user's name and it would tell me when he joined the channel and when he joined a different channel what IP address he was using it'll be hashed and the same thing for Mumble so we'll know when he joined Mumble and if it was with the same IP
So if you ever suspect someone we can just search their name and we'll get a whole report of all their activity
Log out of what
Hmmm just open up an incognito tab
Tested and it looks like it went through
It looks like cloudflare charges $20 a month for WAF per domain. Maybe some of us can look into other options but so far that seems probably the easiest to implement since we're already using it
@Vincent TX another.... Thing to add to the list of tasks is we need to determine the process for backing up the server just in case we lose our host. Do we back up messages and channels or just usernames and passwords and if so where is that stored, etc
653 total messages. Viewing 100 per page.
Prev |
Page 4/7
| Next